Abstract
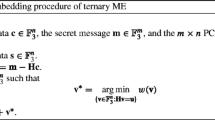
Matrix embedding (ME) is an effective way to reduce the distortion of steganography. In ME, the sender and recipient agree on a matrix in advance, and the message will be embedded into the cover data according to the matrix. By this means, matrices with the same dimension can provide the same capacity but may introduce quite different distortions. Thus the choice of matrices is crucial to the performance of ME and it is meaningful to determine the optimal matrix which can introduce the least distortion. In this paper, we study the optimal-matrix-determination problem for ME in \(\mathbb{F}_3 = \{0,\pm1\}\). Some initial results are obtained.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Fridrich, J.: Steganography in Digital Media: Principles, Algorithms, and Applications. Cambridge University Press, Cambridge (2010)
Li, B., He, J., Huang, J., Shi, Y.Q.: A survey on image steganography and steganalysis. Journal of Information Hiding and Multimedia Signal Processing 2(2), 142–172 (2011)
Fridrich, J.: Minimizing the embedding impact in steganography. In: Proc. 8th ACM Workshop on Multimedia & Security, pp. 2–10 (2006)
Zhang, W., Zhang, X., Wang, S.: Maximizing steganographic embedding efficiency by combining Hamming codes and wet paper codes. In: Solanki, K., Sullivan, K., Madhow, U. (eds.) IH 2008. LNCS, vol. 5284, pp. 60–71. Springer, Heidelberg (2008)
Li, X., Yang, B., Cheng, D., Zeng, T.: A generalization of LSB matching. IEEE Signal Process. Lett. 16(2), 69–72 (2009)
Sallee, P.: Model-based steganography. In: Kalker, T., Cox, I., Ro, Y.M. (eds.) IWDW 2003. LNCS, vol. 2939, pp. 154–167. Springer, Heidelberg (2004)
Cachin, C.: An information-theoretic model for steganography. Information and Computation 192(1), 41–56 (2004)
Pevný, T., Filler, T., Bas, P.: Using high-dimensional image models to perform highly undetectable steganography. In: Böhme, R., Fong, P.W.L., Safavi-Naini, R. (eds.) IH 2010. LNCS, vol. 6387, pp. 161–177. Springer, Heidelberg (2010)
Yang, C.H., Weng, C.Y., Wang, S.J., Sun, H.M.: Adaptive data hiding in edge areas of images with spatial LSB domain systems. IEEE Trans. Inf. Forens. Security 3(3), 488–497 (2008)
Luo, W., Huang, F., Huang, J.: Edge adaptive image steganography based on LSB matching revisited. IEEE Trans. Inf. Forens. Security 5(2), 201–214 (2010)
Gui, X., Li, X., Yang, B.: A content-adaptive ±1-based steganography by minimizing the distortion of first order statistics. In: Proc. IEEE ICASSP, pp. 1781–1784 (2012)
Westfeld, A.: F5–A steganographic algorithm: High capacity despite better steganalysis. In: Moskowitz, I.S. (ed.) IH 2001. LNCS, vol. 2137, pp. 289–302. Springer, Heidelberg (2001)
Fridrich, J., Lisoněk, P., Soukal, D.: On steganographic embedding efficiency. In: Camenisch, J.L., Collberg, C.S., Johnson, N.F., Sallee, P. (eds.) IH 2006. LNCS, vol. 4437, pp. 282–296. Springer, Heidelberg (2007)
Crandall, R.: Some notes on steganography (1998), http://www.dia.unisa.it/ads/corso-security/www/CORSO-0203/steganografia/LINKSLOCALI/matrix-encoding.pdf
Fridrich, J., Soukal, D.: Matrix embedding for large payloads. IEEE Trans. Inf. Forens. Security 1(3), 390–395 (2006)
Khatirinejad, M., Lisoněk, P.: Linear codes for high patload steganography. Discrete Applied Mathematics 157(5), 971–981 (2009)
Gao, Y., Li, X., Yang, B.: Employing optimal matrix for efficient matrix embedding. In: Proc. IIH-MSP, pp. 161–165 (2009)
Cohen, G., Honkala, I., Litsyn, S., Lobstein, A.: Covering Codes. Elsevier, Amsterdam (1997)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Qi, Y., Li, X., Wang, B., Yang, B. (2013). A Study of Optimal Matrix for Efficient Matrix Embedding in \(\mathbb{F}_3\). In: Shi, Y.Q., Kim, HJ., Pérez-González, F. (eds) The International Workshop on Digital Forensics and Watermarking 2012. IWDW 2012. Lecture Notes in Computer Science, vol 7809. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-40099-5_2
Download citation
DOI: https://doi.org/10.1007/978-3-642-40099-5_2
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-40098-8
Online ISBN: 978-3-642-40099-5
eBook Packages: Computer ScienceComputer Science (R0)