Abstract
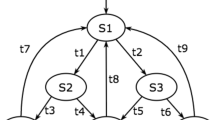
In this paper, we consider how to hide information into finite state machine (FSM), one of the popular computation models. The key advantage of hiding information in FSM is that the hidden information becomes inexpensive to retrieve, yet still hard to remove or delete. This is due to the fact that verifying certain FSM properties is easy, but changing them requires efforts equivalent to redoing all the design and implementation stages after FSM synthesis.
We first observe that not all the FSM specifications (or transitions) are needed during the state minimization phase. We then develop a Boolean Satisfiability (SAT) based algorithm to discover, for a given minimized FSM, a maximal set of redundant specifications. Manipulating such redundancy enables us to hide information into the FSM without changing the given minimized FSM. Moreover, when the original FSM does not possess sufficient redundancy to accommodate the information to be embedded, we propose a state duplication technique to introduce additional redundancy. We analyze these methods in terms of correctness, capacity of hiding data, overhead, and robustness against possible attacks. We take sequential circuit design benchmarks, which adopt the FSM model, as the simulation testbed to demonstrate the strength of the proposed information hiding techniques.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Adelsbach, A., Pfitzmann, B., Sadeghi, A.: Proving Ownership of Digital Content. In: The 3rd International Information Hiding Workshop, September 1999, pp. 126–141 (1999)
Aloul, F., Ramani, A., Markov, I.L., Sakallah, K.A.: Generic ILP versus 0-1 Specialized ILP. In: IEEE/ACM International Conference on Computer Aided Design, June 2002, pp. 450–457 (2002)
Benini, L., Micheli, G.D.: State Assignment for Low Power Dissipation. IEEE Journal of Solid-State Circuits 30, 258–268 (1995)
Craver, S.: Zero Knowledge Watermark Detection. In: The 3rd International Information Hiding Workshop, September 1999, pp. 102–115 (1999)
Hartung, F., Girod, B.: Fast Public-Key Watermarking of Compressed Video. In: IEEE International Conference on Image Processing, pp. 528–531 (October 1997)
Kahng, A.B., et al.: Watermarking Techniques for Intellectual Property Protection. In: 35th Design Automation Conference Proceedings, pp. 776–781 (1998)
Lach, J., Mangione-Smith, W.H., Potkonjak, M.: Fingerprinting Digital Circuits on Programmable Hardware. In: The 2nd International Information Hiding Workshop, April 1998, pp. 16–31 (1998)
Lach, J., Mangione-Smith, W.H., Potkonjak, M.: Signature Hiding Techniques for FPGA Intellectual Property Protection. In: IEEE/ACM International Conference on Computer Aided Design, November 1998, pp. 186–189 (1998)
Lach, J., Mangione-Smith, W.H., Potkonjak, M.: Robust FPGA Intellectual Property Protection Through Multiply Small Watermarks. In: 36th ACM/IEEE Design Automation Conference Proceedings, June 1999, pp. 831–836 (1999)
Moskewicz, M.W., Madigan, C.F., Zhao, Y., Zhang, L., Malik, S.: Chaff: Engineering an Efficient SAT Solver. In: The 38th ACM/IEEE Design Automation Conference, June 2001, pp. 530–535 (2001)
Oliveira, A.L.: Robust Techniques for Watermarking Sequential Circuit Designs. In: 36th ACM/IEEE Design Automation Conference Proceedings, June 1999, pp. 837–842 (1999)
Pfitzmann, B.: Information Hiding Terminology. In: The 1st International Information Hiding Workshop, May 1996, pp. 347–350 (1996)
Qu, G.: Keyless Public Watermarking for Intellectual Property Authentication. In: The 4th International Information Hiding Workshop, April 2001, pp. 96–111 (2001)
Qu, G., Potkonjak, M.: Hiding Signatures in Graph Coloring Solutions. In: The 3rd International Information Hiding Workshop, September 1999, pp. 391–408 (1999)
Qu, G., Potkonjak, M.: Intellectual Property Protection in VLSI Designs: Theory and Practice, January 2003. Kluwer Academic Publishers, Dordrecht (2003)
ILOG Inc. “ILOG AMPL CPLEX System Version 8.0 Use Guide” (2002)
Yang, S.: Synthesis and Optimization Benchmarks User Guide (2002), ftp://mcnc.mcnc.org
Sentovich, E., et al.: SIS: A System for Sequential Circuit Synthesis. Electronics Research Laboratory Memorandum, U.C.Berkeley, No. UCB/ERL M92/41
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Yuan, L., Qu, G. (2004). Information Hiding in Finite State Machine. In: Fridrich, J. (eds) Information Hiding. IH 2004. Lecture Notes in Computer Science, vol 3200. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-30114-1_24
Download citation
DOI: https://doi.org/10.1007/978-3-540-30114-1_24
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-24207-9
Online ISBN: 978-3-540-30114-1
eBook Packages: Computer ScienceComputer Science (R0)