Abstract
Ransomware threat continues to grow over years. The existing defense techniques for detecting malicious malware will never be sufficient because of Malware Persistence Techniques. Packed malware makes analysis harder & also it may sound like a trusted executable for evading modern antivirus. This paper focuses on the analysis part of few ransomware samples using different reverse engineering tools & techniques. There are many automated tools available for performing malware analysis, but reversing it manually helped to write two different patches for Wannacry ransomware. Execution of patched ransomware will not encrypt the user machine. Due to new advanced evading techniques like Anti-Virtual Machine (VM) & Anti-debugging, automated malware analysis tools will be less useful. The Application Programming Interface (API) calls which we used to create patch, were used to create Yara rule for detecting different variants of the same malware as well.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Continella, A., et al.: ShieldFS: a self-healing, ransomware-aware filesystem. In: Proceedings of the Annual Computer Security Applications Conference, ACSAC, Los Angeles, CA (2016)
Gazet, A.: Comparative analysis of various ransomware virii. J. Comput. Virol. 6(1), 77–90 (2010)
Memory dump of VM using vboxmanage blog. https://www.andreafortuna.org/forensics/how-to-extract-a-ram-dump-from-a-running-virtualbox-machine/
Stack strings recovery fireeye blog. https://www.fireeye.com/blog/threat-research/2014/08/flare-ida-pro-script-series-automatic-recovery-of-constructed-strings-in-malware.html
Forked malware samples repository. https://github.com/NaveenEzio/malware-samples/tree/master/Ransomware
Noriben github repository. https://github.com/Rurik/Noriben
Running scripts from the command line with idascript blog. http://www.hexblog.com/?p=128
9 best reverse engineering tools for 2018 blog. https://www.apriorit.com/dev-blog/366-software-reverse-engineering-tools
Monnappa, K.A.: Learning Malware Analysis: Explore the Concepts, Tools, and Techniques to Analyze and Investigate Windows Malware (2018)
Malware initial assessment tool. https://www.winitor.com/
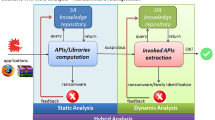
Gregory Paul, T.G., Gireesh Kumar, T.: A framework for dynamic malware analysis based on behavior artifacts. In: Satapathy, S.C., Bhateja, V., Udgata, S.K., Pattnaik, P.K. (eds.) Proceedings of the 5th International Conference on Frontiers in Intelligent Computing: Theory and Applications. AISC, vol. 515, pp. 551–559. Springer, Singapore (2017). https://doi.org/10.1007/978-981-10-3153-3_55
Ali, P.D., Kumar, T.G.: Malware capturing and detection in dionaea honeypot. In: Power and Advanced Computing Technologies (i-PACT) (2017)
Nieuwenhuizen, D.: A behavioural-based approach to ransomware detection. MWR labs whitepaper (2017)
Wannacry ransomware analysis blog. https://www.fireeye.com/blog/threat-research/2017/05/wannacry-malware-profile.html
Unpacking cerber ransomware video. https://www.youtube.com/watch?v=g3Cf3cfBxKM
Stack solver tool github repository. https://github.com/fireeye/flare-floss
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Naveen, S., Gireesh Kumar, T. (2019). Ransomware Analysis Using Reverse Engineering. In: Singh, M., Gupta, P., Tyagi, V., Flusser, J., Ören, T., Kashyap, R. (eds) Advances in Computing and Data Sciences. ICACDS 2019. Communications in Computer and Information Science, vol 1046. Springer, Singapore. https://doi.org/10.1007/978-981-13-9942-8_18
Download citation
DOI: https://doi.org/10.1007/978-981-13-9942-8_18
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-13-9941-1
Online ISBN: 978-981-13-9942-8
eBook Packages: Computer ScienceComputer Science (R0)